Cybersecurity professionals to support critical businesses on their journey
Risk Assessment: identify and prioritize cyber-risks
Control systems and products implemented by nuclear power plants are going increasingly digital and computerized like most of industrial activities. As a consequence, the risk for cybersecurity threats is increasing too. As an industrial player you need to identify and manage the cyber risks targeting your production environment.
Framatome Cybersecurity solutions begin with assessing risks within our customers’ operations, and developing strategies for governance, licensing if needed, and impact planning. For over 60 years Framatome has been designing and maintaining power plants and building instrumentation and control systems for all types of industrial facilities. We know about the unique needs and challenges of control system security that critical asset owners face every day.
Framatome recommends performing a cybersecurity risk analysis based on state-of-the-art international standards in order to map your Instrumentation & Control critical assets, identify and prioritize the cybersecurity major risks, and mitigate those risks with a risk treatment plan.

Penetration testing: simulate a cyberattack
In order to prevent unauthorized access to your industrial processes, you need to identify the critical weaknesses on your IT/OT systems (ie. Computers, systems, network devices, IoT…). Those vulnerabilities could indeed be exploited by a potential attacker to gain access and perform malicious activity.
With worldwide expertise and a proven track record for reliability and performance for over 60 years, Framatome designs, services and installs components, fuel and instrumentation and control systems for all types of nuclear power plants. We understand the unique needs and challenges of control system security that critical asset owners face every day.

Framatome’s security experts have extensive experience in software and network security. They will assist you understanding your threat landscape, assessing your attack surface, identifying vulnerabilities, and implementing countermeasures.
The Framatome Cybersecurity approach to technical audit and penetration testing is built on decades of experience developing and implementing cybersecurity solutions and expertise in industrial information systems.
Our understanding of the potential impacts to customer business during actual attacks, along with the breadth of our technology and expert knowledge of the latest cyber threats, allows our team to conduct tailored attacks on your environment, and develop mitigation plans to prevent such an attack.
System Hardening: reduce your attack surface
In their “out of the box” versions, Operating Systems (Windows, Linux…) could be easily exploited by an internal or external attacker to perform malicious activities. System hardening aims at reducing the attack surface that a potential attacker could take advantage of.
Framatome Cybersecurity can help you “harden” your Operating Systems before they go into production. Systems hardening helps you reduce security risks by eliminating potential attack vectors and reduce the attack surface. By removing unused programs, functions, or applications, attackers and malware have less opportunities to gain access within your infrastructure.
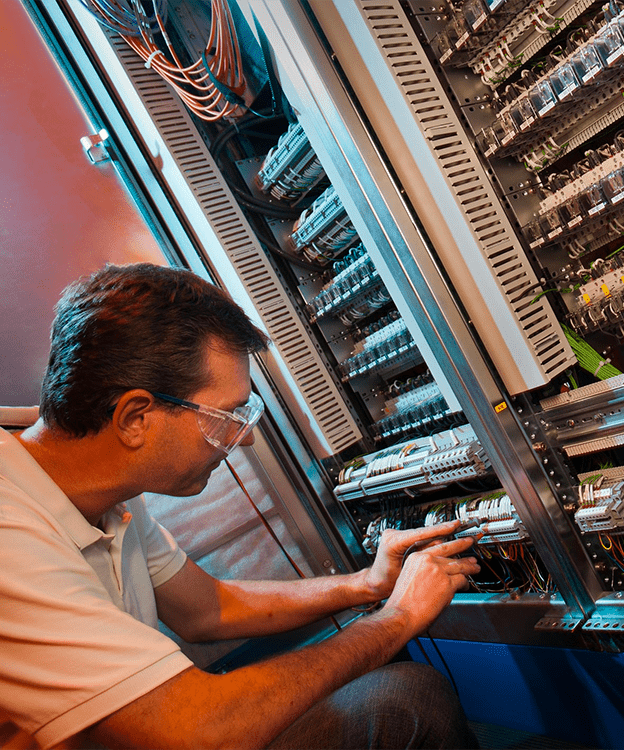
Detect and manage physical intrusions on I&C systems
Reliable long-term support of instrumentation and control (I&C) systems is essential for the safe and economic operation of industrial facilities. Plant protection, control, supervision and monitoring rely on systems that must be completely resistant to tampering or other intrusions. Industrial players need a system that will ensure the integrity of their I&C equipment.
Designed specifically for industrial players, TAG4TRUST is an easy-to-use solution to detect, centralize and monitor physical intrusions on I&C systems. With a simple touchpad, the on-site operator can scan a label and report any event (eg: intrusion, planned intervention, etc…) in the TAG4TRUST app. All events are then signaled to the TAG4TRUST administrator and logged in the central database. The platform also generates intrusion reports that can possibly be used as legal evidence. Tag4Trust allows plant operators to detect any attempt at unauthorized access using controls to trace the tamper proof seals’ integrity. Traceability is assured for you I&C systems and their components, like I&C Cabinet doors, I&C Hardware components or Unprotected communication ports.
Any question? Contact us!
Tag4Trust is an essential tool for any organization looking to improve their cybersecurity posture and stay ahead of potential threats. Don’t hesitate to contact us to request a personalized demo!
